Cybersecurity for Water Operations

Active Protection in Action
Cybersecurity in the Water Sector
The water sector is a critical infrastructure that ensures safe drinking water and wastewater treatment for communities. For decades, the primary focus was on physical safety and reliability. Cybersecurity, however, was often overlooked, with SCADA and process control systems operating on legacy protocols without adequate protection.
As global cyberattacks against critical infrastructure increase, water utilities are now recognising that digital threats can compromise safety, disrupt services, and erode public trust just as much as physical hazards.
Customer Profile
- 2 treatment plants and 9 reservoirs
- 10,000 assets
- 2 automation engineers and no IT/Cyber team on-site
- Numerous third-party contractors
Wastewater Treatment Process and Key Challenges
Wastewater treatment plants rely on SCADA systems, PLCs, sensors, and pumps to ensure clean water processing. The interconnected nature of these systems creates multiple operational challenges that require robust protection.
Unauthorised Remote Access
Challenge: Remote users required connectivity to the plant's jump host for legitimate maintenance and operations, but the risk of unauthorised attempts to send malicious commands to PLCs needed to be prevented.
Malicious Outcome: If attackers gained entry to the jump host, they could issue malicious commands to pumps or valves, leading to sewage overflow or untreated discharge.
First Watch® Solution: The PLC Guards filter all commands sent from the jump host to PLCs, ensuring only authorised and validated instructions are executed. Any unauthorised or unexpected attempt is blocked before reaching the PLC.
Malware & Ransomware on SCADA Computers
Challenge: SCADA workstations were vulnerable to malware infections and ransomware attacks.
Malicious Outcome: Entire treatment plants could be locked down, halting wastewater purification.
First Watch® Solution: ControlGuards with rule-based protection ensure only approved applications run, blocking malicious software before execution.
Manipulation of Process Data
Challenge: Critical process values like tank levels and flow rates could be altered to mislead operators.
Malicious Outcome: Operators might unknowingly release contaminated or insufficiently treated water.
First Watch® Solution: The PLC Guards filter all communications to PLCs, allowing only authorised hosts to send write or read commands. This prevents falsified data injection and ensures process integrity.
PLC Reprogramming Attempts
Challenge: PLCs were exposed to the risk of unauthorised logic changes.
Malicious Outcome: Pumps and valves could be forced into unsafe states, damaging equipment or causing outages.
First Watch® Solution: Active Protection on PLC Guard enforces PLC logic integrity by blocking any unauthorised reprogramming attempts and supporting engineering change management enforcement. Only approved, documented changes are permitted, ensuring operational control and compliance with engineering standards.
Lateral Movement from IT to OT
Challenge: Weak separation between IT and OT networks increased the chance of attack spread.
Malicious Outcome: Corporate breaches could cascade into plant operations, causing downtime and financial loss.
First Watch® Solution: The PLC Guards isolate OT assets from IT threats and block unauthorised cross-network activity.
Why Active Protection Instead of Monitoring
Traditional monitoring solutions rely on detecting anomalies and alerting engineers, which creates several challenges:
- Requires a team of cybersecurity specialists to interpret alerts
- Generates high volumes of false positives, leading to alarm fatigue
- Often reacts too late, after malicious activity has already impacted operations
Recognising these limitations, the water company chose Active Protection with First Watch®. This approach stops malicious activity immediately instead of merely flagging it for later review.
Typical First Watch® Platform Architecture
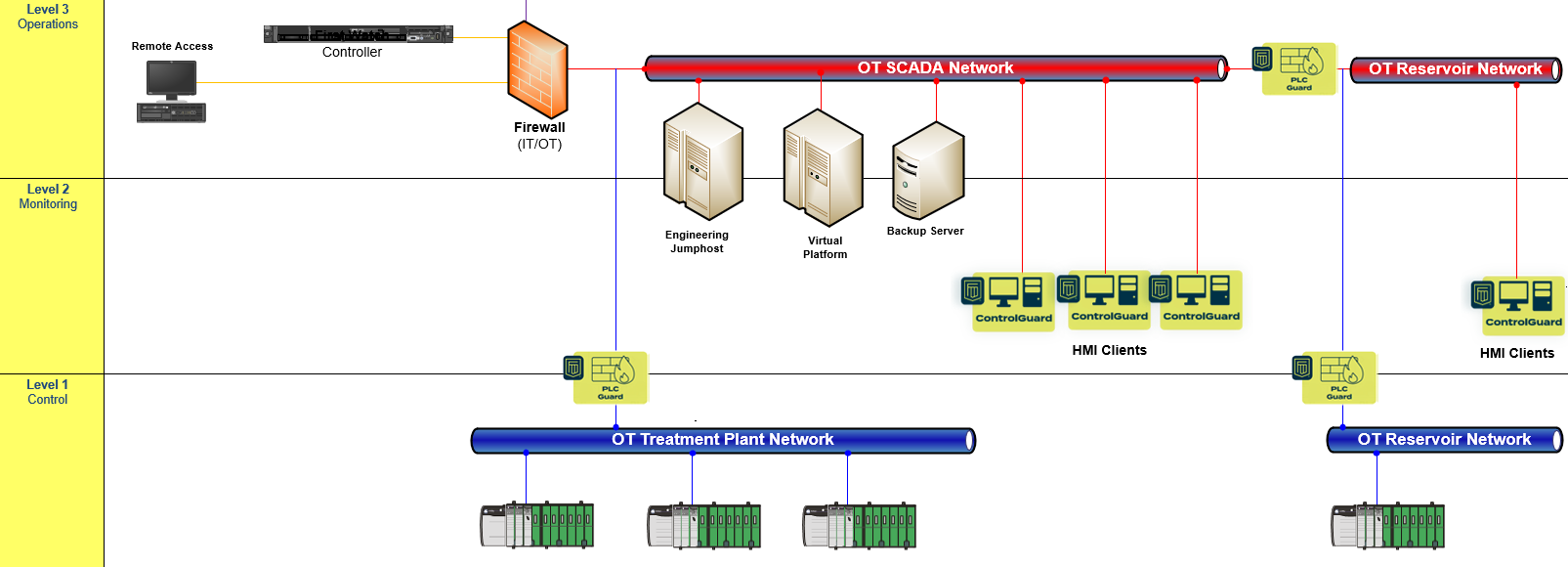
- Controller — central server collecting data and distributing rules
- ControlGuard — endpoint agent preventing unauthorised software on SCADA
- PLC Guard — network agent preventing unauthorised communication with PLC by Deep Packet Inspection (DPI)
How Active Protection Works for SCADA Computers and PLCs
First Watch® deploys rule-based protection directly into the control environment:
- SCADA Computers — First Watch® blocks unauthorised software execution, prevents malware from gaining persistence, and ensures only approved applications run
- PLCs — active protection enforces strict control logic integrity. Any attempt to modify PLC programs or issue unauthorised commands is automatically blocked
- Network Communications — rules ensure only valid commands and expected data flows between devices. Suspicious or out-of-sequence traffic is stopped at once
Unlike machine learning or anomaly-based tools, First Watch®'s deterministic, rule-based engine eliminates false positives by only enforcing what is explicitly allowed. This makes protection transparent to operators while ensuring maximum reliability.
What We Monitor — Water Operations Specifics
Water and wastewater treatment plants typically rely on Allen-Bradley (Rockwell Automation) PLCs communicating over the CIP (Common Industrial Protocol) network. First Watch® provides deep visibility and protection at the protocol level, understanding the specific operations that are critical in water treatment environments.
CIP Protocol Monitoring
PLC Guard performs deep packet inspection of CIP traffic to detect and control operations that directly affect water treatment processes:
- Setpoint write operations — detecting changes to dosing rates, flow targets, tank level thresholds, and pressure setpoints that govern treatment quality
- Variable read/write monitoring — tracking all CIP data table access to identify unexpected read or write operations to critical process tags
- Pump and valve commands — monitoring discrete output commands that control pump sequencing, valve positioning, and actuator states
- Analogue output changes — visibility into modifications to variable frequency drive speeds, dosing pump rates, and blower outputs
Allen-Bradley PLC Protection
For Allen-Bradley ControlLogix and CompactLogix controllers deployed across treatment plants and pump stations, First Watch® monitors and controls:
- Firmware updates — blocking unauthorised firmware modifications that could compromise controller behaviour or safety functions
- Software download and upload — preventing unauthorised logic changes to PLCs that govern treatment sequencing, chemical dosing, and safety interlocks
- Connection with elevated privileges — detecting and controlling RSLogix/Studio 5000 engineering sessions that have authority to modify PLC programs
- Change of PLC mode — alarming on transitions between Run, Program, and Remote modes that occur outside approved maintenance windows
- Online edits — monitoring real-time logic modifications that could alter treatment processes while the plant is operating
Engineering Change Management
A critical requirement in water treatment operations is controlled and auditable change management. First Watch® enforces this at the protocol level:
- All PLC programming sessions are logged — recording who connected, when, and from which workstation
- Unauthorised programming attempts are blocked — only approved engineering workstations can initiate logic downloads or online edits
- Maintenance windows are enforced — programming operations can be restricted to defined time windows aligned with approved change requests
- Change provenance is maintained — every modification is tracked with timestamps and attribution, supporting audit and compliance requirements
This ensures that changes to PLC logic follow the plant's formal change management process, preventing ad-hoc modifications that could compromise water quality, safety, or regulatory compliance.
Process-Specific Visibility
Beyond protocol-level monitoring, the platform provides operational context specific to water treatment processes:
- Chemical dosing parameters — monitoring changes to chlorine, fluoride, and coagulant dosing setpoints that directly affect treated water quality
- Pump station sequencing — tracking changes to pump start/stop sequences, duty/standby configurations, and level-based control logic
- Safety interlock states — monitoring high-level alarms, overflow protection, and emergency shutdown conditions
- Telemetry and remote site communication — visibility into data exchange between treatment plants, pump stations, and reservoirs
This industry-specific depth ensures that First Watch® understands the operational meaning of every CIP transaction and can distinguish legitimate water treatment operations from unauthorised or malicious activity.
Benefits
For the Water Utility
- Reduced operational risk and compliance with critical infrastructure regulations
- No need to employ large cybersecurity teams to interpret alerts
- Continuous protection without disruptions to existing workflows
For the Public
- Assurance of safe, uninterrupted water and wastewater services
- Stronger resilience against cyberattacks that could threaten health and the environment
One of the most critical benefits is that Active Protection requires no constant analysis or intervention. Instead, it stops all malicious activity automatically, providing confidence to both operators and citizens that the water supply is secure, reliable, and future proof.
For more information or to discuss a deployment for your water utility, please contact us.